A card payment feels instantaneous. The system behind it is not.
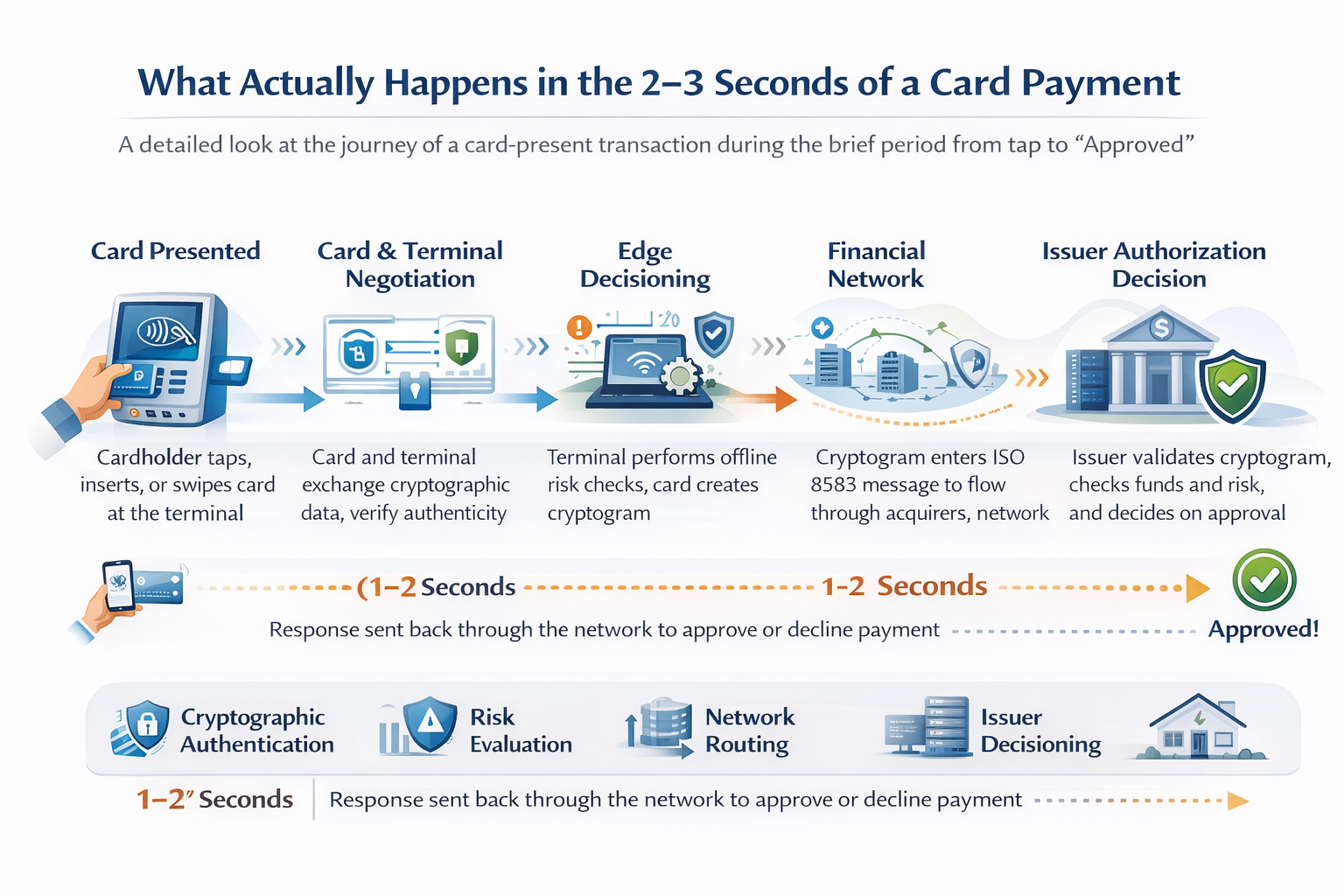
Most people experience a card transaction as a single gesture — tap, beep, approved. What they don’t see is that those 2–3 seconds compress one of the most tightly orchestrated distributed systems in modern commerce: cryptographic authentication, cardholder verification, terminal-side risk management, network routing across multiple financial institutions, real-time issuer decisioning, and a response that travels back through the entire chain before the terminal displays a result.
Every stage has a purpose. Every stage can fail. And if you’re building, certifying, or operating POS systems, understanding what happens in those seconds — and why — is not optional. This post walks through the full lifecycle of a card-present transaction, from the moment the card is presented to the moment the terminal shows “Approved.”
Transaction Initialization: The Terminal and Card Negotiate Trust
The transaction begins the moment a card is presented to the terminal — whether by contactless tap (NFC), chip insertion (ICC), or magnetic stripe swipe. In EMV-based flows, which dominate globally, this first phase is not passive card reading. It is a structured negotiation between two computing devices.
The terminal first detects the interface — contact or contactless — and initiates application selection. The card may support multiple payment applications (Visa credit, Mastercard debit, a domestic scheme), and the terminal selects the appropriate one using the Application Identifier (AID). This selection follows priority rules defined by the terminal configuration, the card’s Application Priority Indicator, and scheme-specific kernel logic. For contactless, the Entry Point specification governs which kernel is activated and how the card is processed.
Once the application is selected, the terminal reads the card’s critical data: the PAN, expiry date, application usage controls, issuer-defined parameters, and the card’s cryptographic capabilities. It also establishes the transaction context — amount, currency, terminal type, terminal capabilities, country code — that will feed into every subsequent decision.
This is the foundation. Everything that follows — authentication, verification, risk analysis, cryptogram generation — depends on the data exchanged in this phase. A misconfigured terminal that reads the wrong tags, selects the wrong application, or misreports its own capabilities will produce downstream failures that are difficult to diagnose.
Card Authentication: Is This Card Genuine?
Before the terminal trusts any data from the card, it needs to establish that the card itself is authentic — that it was legitimately issued and has not been tampered with.
EMV provides three mechanisms for this, in ascending order of strength:
Static Data Authentication (SDA) verifies that the card’s static data (PAN, expiry, issuer-defined data) was signed by the issuer at personalization time. The terminal validates the signature using the issuer’s public key, recovered through the CA public key hierarchy. SDA proves the data has not been altered, but it does not prove uniqueness — a perfect copy of the signed data would pass the same check. SDA is legacy and no longer sufficient for most deployment profiles.
Dynamic Data Authentication (DDA) goes further. The card generates a dynamic signature using its own private key, over data that includes a terminal-generated unpredictable number. The terminal verifies this signature using the card’s ICC public key. Because the signature includes a random challenge, it cannot be replayed or predicted. DDA proves the card possesses a unique private key — which means the card is genuine, not a clone.
Combined DDA with Application Cryptogram (CDA) integrates the dynamic authentication into the cryptogram generation step itself. The card signs the Application Cryptogram (ARQC or TC) together with dynamic data, combining card authentication and transaction authorization into a single cryptographic operation. CDA is the strongest mechanism and is the standard for modern EMV deployments.
The question this phase answers is precise: Is this card a legitimate instrument issued by a real issuer, and can it prove it? Everything downstream — CVM, risk management, authorization — depends on this answer being correct.
Cardholder Verification: Who Is Holding the Card?
Card authentication proves the instrument is genuine. It does not prove the person presenting it is the legitimate cardholder. That is a separate problem, and it is solved by Cardholder Verification Methods (CVM).
The issuer encodes a CVM strategy in the card’s CVM List (tag 8E) — a prioritized list of verification methods and the conditions under which each applies. The terminal walks the list and selects the first method that both parties support and whose condition is satisfied for the current transaction context.
The primary methods:
Online PIN — The cardholder enters their PIN on a PCI-certified PIN Entry Device (PED). The PED encrypts the PIN block immediately — the clear PIN never exists outside the secure hardware. The encrypted PIN block travels through the acquirer to the issuer, where an HSM decrypts and validates it. This is the strongest widely deployed CVM for card-based transactions.
Offline PIN — The card itself verifies the PIN using a reference value stored in secure chip memory. A PIN Try Counter (tag 9F17) limits brute-force attempts at the hardware level. Offline PIN is essential for environments where the terminal cannot always reach the issuer — fuel, transit, rural acceptance, resilience-first architectures. The issuer never sees the PIN; it trusts the chip’s verification result.
Consumer Device CVM (CDCVM) — For mobile wallet transactions (Apple Pay, Google Pay), the cardholder authenticates on the device using biometrics or a device passcode. The wallet cryptogram includes a flag indicating CDCVM was performed. This satisfies the same architectural requirement — strong cardholder verification — with a different interface.
Signature — A human-compared mark with no cryptographic binding to the cardholder. Largely deprecated but still present in some legacy configurations.
No CVM — Used for low-value contactless transactions where the scheme has determined the risk is bounded by the transaction amount and cumulative limits. This is an intentional risk trade-off, not an absence of security.
A critical distinction that is often misunderstood: EMV authenticates the card. CVM authenticates the cardholder. These are two different security problems solved by two different mechanisms in the same flow. Conflating them — treating chip authentication as if it also proves cardholder identity — leads to gaps in the risk model.
Terminal and Card Risk Management: Decisions at the Edge
Before the transaction goes online to the issuer, both the terminal and the card perform independent risk assessments. This is one of the most underappreciated phases of the EMV flow — and one of the most architecturally significant.
Terminal Risk Management
The terminal evaluates the transaction against its own configured rules:
- Floor limit checking. Is the transaction amount above the terminal’s floor limit? If so, the transaction must go online for issuer authorization regardless of other factors.
- Random transaction selection. Even below the floor limit, a configurable percentage of transactions are randomly selected for online authorization. This prevents a pattern where low-value fraud always stays offline and undetected.
- Velocity checking. The terminal can track consecutive offline transactions and force an online authorization after a threshold is reached. This bounds the exposure from cards that have been operating offline for extended periods.
Card Risk Management
The card performs its own checks using issuer-defined parameters stored at personalization:
- Application Transaction Counter (ATC). The ATC increments with every transaction. Issuer-defined thresholds can trigger a requirement to go online after a certain number of offline transactions.
- Offline spending limits. The card tracks cumulative offline amounts (Lower and Upper Consecutive Offline Limits) and can force online authorization when thresholds are exceeded.
- Issuer-defined risk parameters. Additional risk rules encoded in the card’s Application Interchange Profile and Issuer Action Codes.
The combined result of terminal and card risk management produces one of three outcomes:
- Approve offline — both parties are satisfied, and the card generates a Transaction Certificate (TC). The transaction completes without going online.
- Decline offline — the card or terminal determines the transaction cannot be approved. The card generates an Application Authentication Cryptogram (AAC).
- Go online — the most common outcome for attended POS in markets with reliable connectivity. The card generates an ARQC, and the transaction is sent to the issuer for real-time authorization.
The design principle here is layered risk assessment at the edge. The terminal and card don’t blindly forward every transaction to the issuer. They make independent decisions based on local context — and only escalate to the network when conditions require it. This is what makes the system resilient: it can still function, with bounded risk, when connectivity degrades.
Cryptogram Generation: The Cryptographic Heart of the Transaction
If the transaction goes online — and most attended POS transactions do — the card generates the Authorization Request Cryptogram (ARQC). This is the single most important security mechanism in the EMV flow.
The ARQC is an 8-byte MAC computed by the card using a session key derived from the card’s unique key and the current ATC. The inputs to the MAC include the transaction amount, currency, date, terminal country code, Terminal Verification Results (TVR), transaction type, and the Unpredictable Number (tag 9F37) — four random bytes generated by the terminal that add entropy to the cryptogram.
The result is a value that is unique to this specific transaction, on this specific card, at this specific terminal, at this specific moment. It cannot be predicted, replayed, or forged without the secret key embedded in the chip’s secure element.
The issuer independently derives the same session key using its master key hierarchy and recomputes the expected ARQC from the transaction data it receives. If the computed value matches the card’s ARQC, the cryptographic check passes — the card is genuine and the transaction data has not been altered in transit. If it doesn’t match, the transaction is declined.
This is why EMV dramatically reduced counterfeit fraud at the point of sale. With magnetic stripe, the card data was static — copy it once, replay it forever. With EMV, every transaction produces a unique cryptographic proof that cannot be manufactured without the key locked inside the chip. For a deeper treatment of the ARQC mechanism, key hierarchy, and implementation pitfalls, see the companion post on why EMV chip cards resist cloning.
The Network Journey: Terminal to Acquirer to Scheme to Issuer
Once the ARQC is generated and the terminal has completed its local processing, the transaction leaves the physical world and enters the financial messaging network.
The terminal constructs an ISO 8583 authorization request message — the standard message format used across the payment industry. The key data elements include the PAN (DE 2), processing code (DE 3), transaction amount (DE 4), the EMV chip data in TLV-encoded format (DE 55), the encrypted PIN block if applicable (DE 52), and the POS entry mode (DE 22) indicating how the card was read.
DE 55 deserves specific attention. It carries the chip data — ARQC, ATC, TVR, Application Interchange Profile, CDOL-related tags — that the issuer needs to validate the cryptogram. If the acquirer or any intermediary modifies, truncates, or incorrectly re-encodes DE 55, the issuer cannot reconstruct the ARQC input, and the cryptogram verification fails. This is a surprisingly common source of production failures.
The message flows through a well-defined chain:
The acquirer (or its processor) receives the message from the terminal, enriches it with merchant identification and routing data, and forwards it to the appropriate card network.
The card scheme (Visa, Mastercard, or others) acts as the switch — routing the message from the acquirer’s network to the correct issuer based on the BIN (Bank Identification Number) in the PAN. The scheme also applies its own fraud and compliance rules at this stage.
The issuer (or its processor) receives the message and performs the authorization decision.
This entire network journey — terminal to acquirer to scheme to issuer — typically completes in hundreds of milliseconds. The infrastructure that makes this possible is one of the most reliable real-time distributed systems ever built, processing billions of transactions per day across continents with sub-second latency requirements.
Issuer Decisioning: The Authorization Decision
The issuer is where the final authorization decision is made. It evaluates the transaction across multiple dimensions simultaneously.
Cryptographic validation. The issuer (or its HSM) derives the expected session key from the card’s master key and the ATC, recomputes the ARQC from the transaction data in DE 55, and compares it to the card’s submitted value. A match confirms the card is genuine and the data is intact. A mismatch means decline — no ambiguity.
Financial checks. Is there sufficient balance or credit limit? Has the account been flagged for any restrictions? Is the card active and in good standing?
Risk and fraud analysis. Modern issuer systems run real-time risk engines that evaluate velocity patterns (how many transactions in the last hour?), geolocation (is the card being used in a different country than the last transaction?), merchant category (is this a high-risk MCC?), and behavioral scoring — increasingly driven by machine learning models trained on the card portfolio’s transaction history. These checks run in milliseconds and produce a risk score that influences the authorization decision.
Regulatory and business rules. Strong Customer Authentication (SCA) requirements under PSD2 in European markets, MCC-based restrictions, and issuer-specific policies all factor into the decision.
The issuer responds with an authorization response code — approved, declined, or referral — and generates the Authorization Response Cryptogram (ARPC). The ARPC is the issuer’s cryptographic proof back to the card, computed using the ARQC and the authorization response code. When the terminal delivers the ARPC to the card, the card can verify that the response genuinely came from the issuer and was not fabricated or modified in transit.
The Return Path: Completing the EMV Flow
The issuer’s response travels back through the same chain in reverse: issuer to scheme, scheme to acquirer, acquirer to terminal. The response message carries the authorization response code, the ARPC, and optionally issuer scripts — commands that the terminal delivers to the card to update parameters, reset counters, or block the card if needed.
At the terminal, the EMV flow completes:
The terminal delivers the ARPC to the card. The card validates it, confirming the response is authentic. Based on the issuer’s decision and its own Terminal Action Codes, the terminal makes a final determination — and displays the result to the cardholder.
At this exact moment, the authorization is complete. The cardholder sees “Approved” and walks away. The merchant has an authorization code. But the money has not actually moved yet.
After Authorization: Clearing and Settlement
The “Approved” on the terminal screen is the end of authorization — not the end of the financial process.
Clearing happens later, typically in batches. The terminal (or the acquirer’s host) accumulates authorized transactions and submits them for clearing through the card scheme. The clearing message includes the final transaction details and reconciles what was authorized with what is being claimed.
Settlement is the actual movement of funds — from the issuer to the acquirer, less interchange fees and scheme fees. Settlement timelines vary by scheme, acquirer, and market, but T+1 or T+2 is typical for card-present transactions.
This distinction matters for merchants, acquirers, and anyone building reconciliation systems: an authorized transaction can still fail to settle. Reversals, chargebacks, and clearing mismatches are all post-authorization events that can alter the financial outcome. What the cardholder experienced as a completed payment may still be in flux for days.
The System as a Whole
What looks like a tap is actually a distributed system that spans continents and compresses cryptography, risk analysis, financial messaging, and real-time decisioning into a 2–3 second window. Every layer has a purpose:
- EMV at the terminal authenticates the card, verifies the cardholder, and manages risk at the edge
- The ARQC provides per-transaction cryptographic proof that binds the card, the terminal, and the transaction data into an unforgeable authorization request
- The ISO 8583 message carries the transaction through a network of acquirers, schemes, and issuers with sub-second routing
- The issuer validates the cryptogram, runs real-time fraud analysis, and makes the authorization decision
- The ARPC closes the loop — the issuer proves its identity back to the card
The system works because each participant does its job within a well-defined protocol. The card proves itself to the terminal. The terminal proves the transaction to the acquirer. The acquirer routes it to the issuer. The issuer validates and responds. And the cryptographic thread — ARQC out, ARPC back — ensures that no participant can forge or tamper with the exchange without detection.
Billions of times per day, across millions of devices, networks, and issuers, this system is secure enough to prevent fraud, fast enough to feel instantaneous, and reliable enough that people never think about it.
Until something breaks. And when it does, every engineer in payments is reminded: those 2–3 seconds are anything but simple.
Further Reading
- Why EMV Chip Cards Resist Cloning: The ARQC Mechanism Explained — deep dive into the cryptogram that makes this system work
- EMV Cryptograms: How ARQC Prevents Fraud — full technical treatment: key hierarchy, session key derivation, ARPC response, CDOL1 structure
- Why PIN Still Matters in Card-Present Payments — the CVM layer explained
- EMV for Developers — the three pillars of EMV from a developer-centric perspective
- EMVCo Book 2: Security and Key Management
- EMVCo Book 3: Application Specification — GENERATE AC, CVM List, Terminal and Card Risk Management
- EMVCo Book 4: Cardholder, Attendant, and Acquirer Interface Requirements
- ISO 8583 — Financial transaction card originated messages
- Point-of-Sale Systems Architecture — Volume 1: A Practical Guide to Secure, Certifiable POS Systems